Hackers have spiritual eroticismdiscovered a new way to remotely take control of your computer — all through the Google Chrome web browser.
A report from cybersecurity company SquareX lays out the new multifaceted cyberattack, which the firm has dubbed "browser syncjacking."
At the core of the attack is a social engineering element, as the malicious actor first must convince the user to download a Chrome extension. The Chrome extension is usually disguised as a helpful tool that can be downloaded via the official Chrome Store. It requires minimal permissions, further cementing its perceived legitimacy to the user. According to SquareX, the extension actually does usually work as advertised, in order to further disguise the source of the attack from the user.
Meanwhile, secretly in the background, the Chrome extension connects itself to a managed Google Workspace profile that the attacker has set up in advance. With the user now unknowingly signed into a managed profile, the attacker sends the user to a legitimate Google support page which is injected with modified content through the Chrome extension, telling the user they need to sync their profile.
When the user agrees to the sync, they unwittingly send all their local browser data, such as saved passwords, browsing history, and autofill information, to the hacker's managed profile. The hacker can then sign into this managed profile on their own device and access all that sensitive information.
The attack up to this point already provides the hacker with enough material to commit fraud and other illicit activities. However, browser syncjacking provides the hacker with the capability to go even further.
Using the teleconferencing platform Zoom as an example, SquareX explains that using the malicious Chrome extension, the attacker can send the victim to an official yet modified Zoom webpage that urges the user to install an update. However, the Zoom download that's provided is actually an executable file that installs a Chrome browser enrollment token from the hacker's Google Workspace.
After this occurs, the hacker then has access to additional capabilities and can gain access to the user's Google Drive, clipboard, emails, and more.
The browser syncjacking attack doesn't stop there. The hacker can take one further step in order to not just take over the victim's Chrome profile and Chrome browser, but also their entire device.
Through that same illicit download, such as the previously used Zoom update installer example, the attacker can inject a "registry entry to message native apps" by weaponizing Chrome’s Native Messaging protocol. By doing this, the attacker basically sets up a connection "between the malicious extension and the local binary." Basically, it creates a flow of information between the hacker's Chrome extension and your computer. Using this, the hacker can send commands to your device.
What can the hacker do from here? Pretty much anything they want. The attacker will have full access to the user's computer files and settings. They can create backdoors into the system. They can steal data such as passwords, cryptocurrency wallets, cookies, and more. In addition, they can track the user by controlling their webcam, take screenshots, record audio, and monitor everything input into the device.
As you can see, browser syncjacking is nearly completely unrecognizable as an attack to most users. For now, the most important thing you can do to protect yourself from such a cyberattack is to be aware of what you download and only install trusted Chrome extensions.
Topics Cybersecurity Google
 Best GPU deal: Get the MSI RTX 5080 for $1,249.99 at Best Buy
Best GPU deal: Get the MSI RTX 5080 for $1,249.99 at Best Buy
 Alternative Routes: A Conversation with Lauren Elkin by Claire
Alternative Routes: A Conversation with Lauren Elkin by Claire
 Samsung Galaxy S24 series comes with Google's Gemini AI model
Samsung Galaxy S24 series comes with Google's Gemini AI model
 Redux: Too Sweet a Muddle by The Paris Review
Redux: Too Sweet a Muddle by The Paris Review
 Skinning a Cat: On Writer’s Block by The Paris Review
Skinning a Cat: On Writer’s Block by The Paris Review
 En Garde by The Paris Review
En Garde by The Paris Review
 All major streaming platforms will support Apple Vision Pro — except Netflix
All major streaming platforms will support Apple Vision Pro — except Netflix
 Quiet Magic by The Paris Review
Quiet Magic by The Paris Review
 Strangers and the Moon by The Paris Review
Strangers and the Moon by The Paris Review
 The Samsung S24 Ultra's Titanium Yellow is a runway
The Samsung S24 Ultra's Titanium Yellow is a runway
 How to watch Samsung Unpacked: Galaxy S24, Galaxy AI awaits
How to watch Samsung Unpacked: Galaxy S24, Galaxy AI awaits
 The White House might have inflated Trump's golf record, because this is how we live now
The White House might have inflated Trump's golf record, because this is how we live now
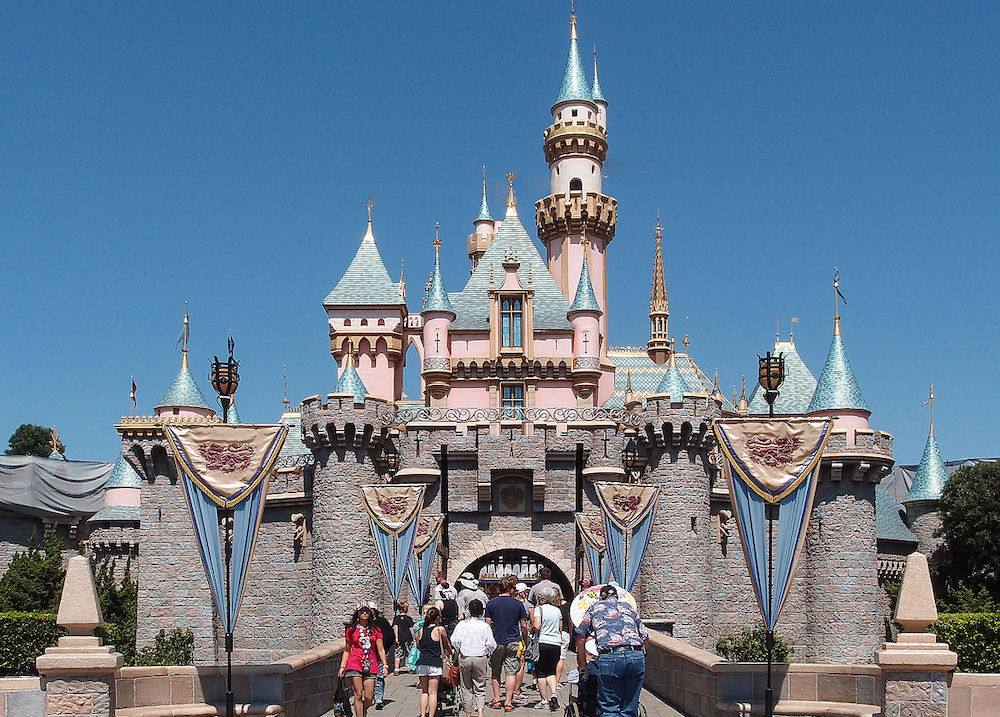 The Happiest Place on Earth? by Albert Samaha
The Happiest Place on Earth? by Albert Samaha
 Nocturne Vibes by The Paris Review
Nocturne Vibes by The Paris Review
 Best free online courses from UC Berkeley
Best free online courses from UC Berkeley
 A Woman and a Philosopher: An Interview with Amia Srinivasan by Lidija Haas
A Woman and a Philosopher: An Interview with Amia Srinivasan by Lidija Haas
These stunning Danish treats are inspired by Brutalist architectureJennifer Lawrence says she's iffy on doing an Oscars interview with Ryan SeacrestEquifax admits additional 2.4 million Americans affected by 2017 hackBody positivity isn't enough. This book will teach you 'radical' selfMarvel's 'Avengers: Infinity War' is coming sooner than we thoughtAly Raisman sues U.S. Olympic Committee and USA Gymnastics for how they dealt with Nassar abuseMen in Hollywood launch campaign to support sexual assault survivorsGoogle Chrome's new 'Song Maker' lets you make music in your browserOtter app transcribes any verbal conversation into searchable textThere's currently no interracial couple emoji. Tinder wants to change that.Unreleased teenage Amy Winehouse demo emerges, titled "My Own Way"Bitcoin's selfHere's what Vero's founder has to say about its overnight successThis phone company is turning heads by being more ambitious than AppleWaltonchain token crashes following sketchy tweet7 animated feature films that deserved more attention than their Oscar competitionEnterprising food blogger figures out how to make wine in an Instant PotThe best tech of Mobile World Congress 2018Alexa is down on Amazon Echo speakersAmazon buys smart doorbell iPhone users in 92 countries received a spyware attack alert How Prime Video's 'Fallout' successfully incorporates game details into the TV show Judge tosses out another climate suit in NYC. What comes next? Crypto and taxes: Which forms you need to file Meta tests tools to protect teens from sextortion and unwanted nude photos Geely’s EV brand Zeekr enters the Kazakhstan market · TechNode Chery becomes first automaker to use Huawei’s latest OS · TechNode iMile Delivery enters Italy, becomes first Chinese delivery startup to enter Europe · TechNode TSMC to eat costs of defective 3nm chips under new agreement with Apple · TechNode Google Photos is making its AI photo editing tools available for all users Researchers map the koala genome in the name of saving the species 'Fallout' gives a major 'New Vegas' hint in the finale WeChat beta tests Xiaohongshu How to take a screenshot on an iPad Biden imposes restrictions on US investment in China’s sensitive tech industry · TechNode Chinese VR company iQiyi Smart fails to pay employees amid cash flow disruption · TechNode Best free online courses from Georgia Tech Amazon deals of the day: Galaxy Tab S6 Lite, Galaxy Book4 Pro, Fire TV Stick 4k Max, and more Tencent begins AI model beta tests · TechNode ByteDance tests AI chatbot Grace, says it’s still immature · TechNode
1.8377s , 8287.140625 kb
Copyright © 2025 Powered by 【spiritual eroticism】,Steady Information Network