Hackers have sex video situationdiscovered a new way to remotely take control of your computer — all through the Google Chrome web browser.
A report from cybersecurity company SquareX lays out the new multifaceted cyberattack, which the firm has dubbed "browser syncjacking."
At the core of the attack is a social engineering element, as the malicious actor first must convince the user to download a Chrome extension. The Chrome extension is usually disguised as a helpful tool that can be downloaded via the official Chrome Store. It requires minimal permissions, further cementing its perceived legitimacy to the user. According to SquareX, the extension actually does usually work as advertised, in order to further disguise the source of the attack from the user.
Meanwhile, secretly in the background, the Chrome extension connects itself to a managed Google Workspace profile that the attacker has set up in advance. With the user now unknowingly signed into a managed profile, the attacker sends the user to a legitimate Google support page which is injected with modified content through the Chrome extension, telling the user they need to sync their profile.
When the user agrees to the sync, they unwittingly send all their local browser data, such as saved passwords, browsing history, and autofill information, to the hacker's managed profile. The hacker can then sign into this managed profile on their own device and access all that sensitive information.
The attack up to this point already provides the hacker with enough material to commit fraud and other illicit activities. However, browser syncjacking provides the hacker with the capability to go even further.
Using the teleconferencing platform Zoom as an example, SquareX explains that using the malicious Chrome extension, the attacker can send the victim to an official yet modified Zoom webpage that urges the user to install an update. However, the Zoom download that's provided is actually an executable file that installs a Chrome browser enrollment token from the hacker's Google Workspace.
After this occurs, the hacker then has access to additional capabilities and can gain access to the user's Google Drive, clipboard, emails, and more.
The browser syncjacking attack doesn't stop there. The hacker can take one further step in order to not just take over the victim's Chrome profile and Chrome browser, but also their entire device.
Through that same illicit download, such as the previously used Zoom update installer example, the attacker can inject a "registry entry to message native apps" by weaponizing Chrome’s Native Messaging protocol. By doing this, the attacker basically sets up a connection "between the malicious extension and the local binary." Basically, it creates a flow of information between the hacker's Chrome extension and your computer. Using this, the hacker can send commands to your device.
What can the hacker do from here? Pretty much anything they want. The attacker will have full access to the user's computer files and settings. They can create backdoors into the system. They can steal data such as passwords, cryptocurrency wallets, cookies, and more. In addition, they can track the user by controlling their webcam, take screenshots, record audio, and monitor everything input into the device.
As you can see, browser syncjacking is nearly completely unrecognizable as an attack to most users. For now, the most important thing you can do to protect yourself from such a cyberattack is to be aware of what you download and only install trusted Chrome extensions.
Topics Cybersecurity Google
 Best Dyson deal: Save $320 on the Dyson Zone Active Noise
Best Dyson deal: Save $320 on the Dyson Zone Active Noise
 Hunter’s Moon by Nina MacLaughlin
Hunter’s Moon by Nina MacLaughlin
 Thanksgiving with John Ehle by Valerie Stivers
Thanksgiving with John Ehle by Valerie Stivers
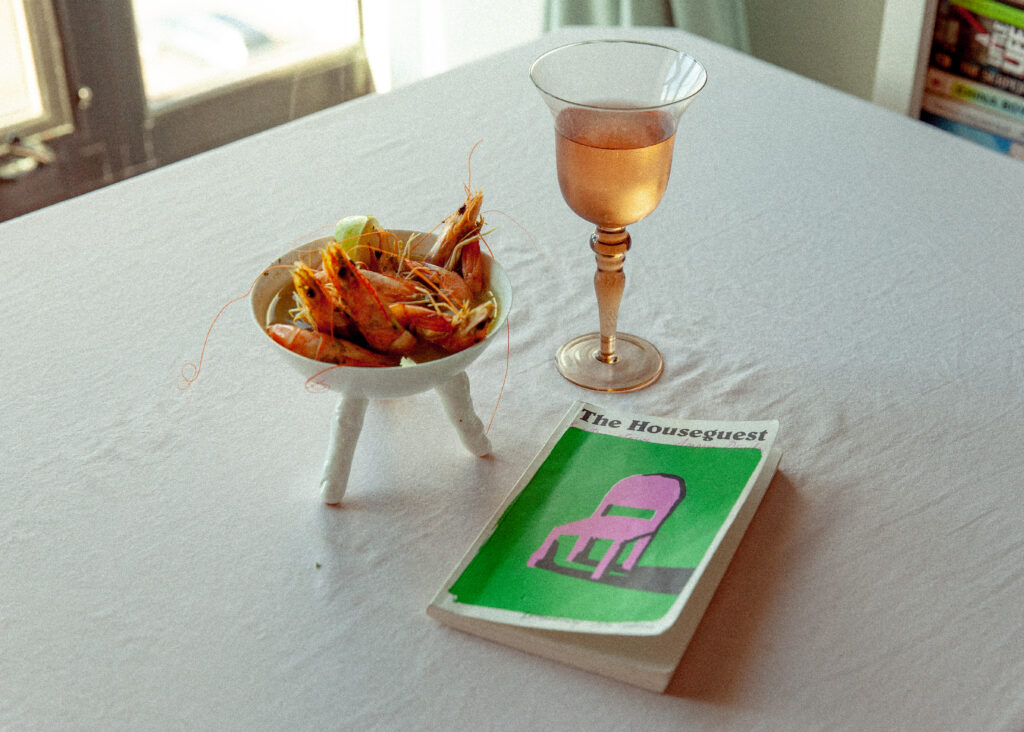 Cooking with Amparo Dávila by Valerie Stivers
Cooking with Amparo Dávila by Valerie Stivers
 Why Spotify's 'daylist' is all over Instagram stories
Why Spotify's 'daylist' is all over Instagram stories
 Nocturne Vibes by The Paris Review
Nocturne Vibes by The Paris Review
 Even Trump's Earth Day message was anti
Even Trump's Earth Day message was anti
 All major streaming platforms will support Apple Vision Pro — except Netflix
All major streaming platforms will support Apple Vision Pro — except Netflix
 How I met my partner on X/Twitter
How I met my partner on X/Twitter
 The Samsung S24 Ultra's Titanium Yellow is a runway
The Samsung S24 Ultra's Titanium Yellow is a runway
 Best Dyson deal: Save $320 on the Dyson Zone Active Noise
Best Dyson deal: Save $320 on the Dyson Zone Active Noise
 Sentience and Intensities: A Conversation with Maureen McLane by Anahid Nersessian
Sentience and Intensities: A Conversation with Maureen McLane by Anahid Nersessian
 Best Samsung Galaxy Watch Ultra deal: Save $200 at Best Buy
Best Samsung Galaxy Watch Ultra deal: Save $200 at Best Buy
 The best Samsung Galaxy S24 Ultra preorder deals you can get right now
The best Samsung Galaxy S24 Ultra preorder deals you can get right now
 Best Dyson deal: Save $320 on the Dyson Zone Active Noise
Best Dyson deal: Save $320 on the Dyson Zone Active Noise
 Wild Apples by Lauren Groff
Wild Apples by Lauren Groff
 New, Tender, Quick: A Visit to the Elizabeth Bishop House by Henri Cole
New, Tender, Quick: A Visit to the Elizabeth Bishop House by Henri Cole
Philip Connors on 'Fire Season' by Maud Newton“Lit It Crowd” Lousy with Parisians by Lorin SteinNASA spacecraft snaps photos of the most mysterious asteroidsJoin us at the Norwood by Thessaly La ForceHello, Brave New WorldGuilt by AssociationOuter Space; Dad Books by Lorin SteinMr. Grift Goes to WashingtonDavid Orr: Lost in the Archives, Spring 1974 by David OrrHello, Brave New WorldPut Up This Wall! by David ZaxNostalgia ActTerritorial PissingFeminist FascismsSmall FryPut Up This Wall! by David ZaxTwitch updates: Vertical video and dual streamingHello, Brave New WorldBiden’s Final HumiliationThe Southwest Syndrome The Paris Review Podcast, Episode 20 by The Paris Review Oranges by Jordan Kisner A Dispatch from Emily Stokes, Editor by Emily Stokes Tolstoy’s Uncommon Sense and Common Nonsense by Yiyun Li Committed to Memory: Josephine Halvorson and Georgia O'Keeffe by Charlotte Strick Remembering Jan Morris Authenticity and Apocalypse: An Interview with Alexandra Kleeman by Cornelia Channing Redux: In Honor of Jamaica Kincaid by The Paris Review Illuminate I Could: On Lucille Clifton by Tracy K. Smith All You Have to Do Is Die by Rowan Hisayo Buchanan Hunter’s Moon by Nina MacLaughlin Dodie Bellamy’s Many Appetites by Emily Gould Freedom from Sugarcane Hell: An Interview with Vinod Busjeet by Parul Kapur Hinzen Jim Jarmusch’s Collages by Lucy Sante Wild Apples by Lauren Groff The Ghosts of Sittwe by Thirii Myo Kyaw Myint Redux: Too Sweet a Muddle by The Paris Review Allowing Things to Happen: An Interview with Tyshawn Sorey by Craig Morgan Teicher Redux: It’s All a Question of Language by The Paris Review The Fourth Rhyme: On Stephen Sondheim by Adrienne Raphel
3.2863s , 8612.8125 kb
Copyright © 2025 Powered by 【sex video situation】,Steady Information Network